In an increasingly connected world, where businesses rely heavily on digital aspects such as e-commerce, telecommuting, cloud services and distributed asset control, software quality and security have become critical to business survival and success. A lack of quality and/or a security breach can have serious consequences, from loss of confidential data to damage to brand reputation and even disruptions to operations.
Cybercrime represents a significant economic challenge, with an estimated annual cost of $10.5 billion. In addition, around 90 million attacks are recorded each year. In Spain, during 2022, more than 375,000 crimes were committed over the Internet, meaning that 1 in 5 crimes in the country occurred online. This situation highlights the urgent need to strengthen cybersecurity and protection measures in the digital sphere.
At SIPSA, we understand that absolute security against cyber-attacks is not achievable. However, our goal is to help you achieve the highest level of security and confidence in your software. We are an expert consultancy in digital transformation, software quality and automated testing. We have defined the SPHERICAL QUALITY methodology, a model that will enable you to develop secure, reliable, and quality software.
Where do we act to achieve quality and secure software?
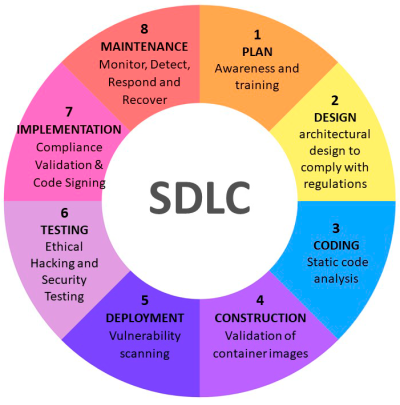
At every stage of the software development lifecycle, quality and security practices are integrated. From planning to implementation, criteria are established to ensure that the software meets high standards and prevents vulnerabilities.
- PLAN: Awareness and training.

Awareness and training of the team are crucial to create a culture of quality and security in the organization. Employees must understand the most common cyber threats, secure coding practices, sensitive data management and the importance of security testing. - DESIGN: Secure architecture design.
A solid and well-designed architecture is the basis of a secure system. At this stage, secure design principles are defined, a threat analysis is performed, security layers are implemented, etc.
- CODING: Static code analysis.
This process is a powerful tool to identify potential vulnerabilities, bugs and areas for improvement in the code before they are implemented in production. By addressing problems at the source, a solid and secure foundation for the software is ensured. Contributing to software quality. - CONSTRUCTION: Validation of container images.
Container images are essential components for the implementation and execution of applications. At this stage, the origin of the images is verified, their digital signature is validated, the file used to build the image is examined, constant updating of the images is ensured, and their use is logged and audited.
Vulnerability scanning allows the identification and prioritisation of security risks in the software before its deployment in production. This process seeks to detect flaws such as loss of access control, cryptographic flaws, code injection, insecure design, identification and authentication flaws, software and data integrity flaws, and server-side request forgery. Scanning should be automated and should generate regular reports for decision making. - TESTING: Ethical Hacking and Security Testing.
Ethical hacking and security testing are advanced techniques to assess the resilience of systems to real cyber-attacks. These tests are conducted by experts who simulate real attacks to identify vulnerabilities that might go undetected in automated tests. - IMPLEMENTATION: Compliance Validation and Code Signing.
Compliance validation ensures that the software complies with applicable standards and regulations. Code signing allows to verify the integrity of the software and to prevent the execution of unsigned or untrusted code. In addition, internal security policies should be established, and regular compliance audits should be performed. - MAINTENANCE: MDRR (Monitor, Detect, Respond and Recover).
MDRR is a continuous process for security incident management. It includes the constant monitoring of systems, networks and applications for suspicious activity or indicators of compromise. If an incident is detected, it must be responded to quickly and effectively to contain the damage and prevent further exposure. The final phase is the recovery of affected systems to a normal operational state.
The SPHERICAL QUALITY methodology is a comprehensive and revolutionary strategy that enables companies to protect their software and digital assets in an increasingly complex and threatening world. By addressing security from the earliest stages of development through to ongoing maintenance, organizations can mitigate risks and ensure the quality, reliability, and stability of their applications. Not only do they protect their data and their customers’ privacy, but they also foster a culture of security among their teams. This culture of security promotes customer confidence and enhances brand reputation, giving companies a competitive advantage in the marketplace.
SIPSA, as a pioneer in the application of SPHERICAL QUALITY, becomes a valuable ally for companies looking to succeed in the digital age. With an approach based on prevention, early detection, and rapid response to threats, SIPSA offers its customers the confidence that their software is secure, reliable, and ready to meet future challenges. This enables businesses to thrive and achieve sustainable success in an ever-evolving digital environment.




Leave A Comment
You must be logged in to post a comment.